this post was submitted on 08 Aug 2024
1504 points (99.2% liked)
Programming
17020 readers
244 users here now
Welcome to the main community in programming.dev! Feel free to post anything relating to programming here!
Cross posting is strongly encouraged in the instance. If you feel your post or another person's post makes sense in another community cross post into it.
Hope you enjoy the instance!
Rules
Rules
- Follow the programming.dev instance rules
- Keep content related to programming in some way
- If you're posting long videos try to add in some form of tldr for those who don't want to watch videos
Wormhole
Follow the wormhole through a path of communities !webdev@programming.dev
founded 1 year ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments

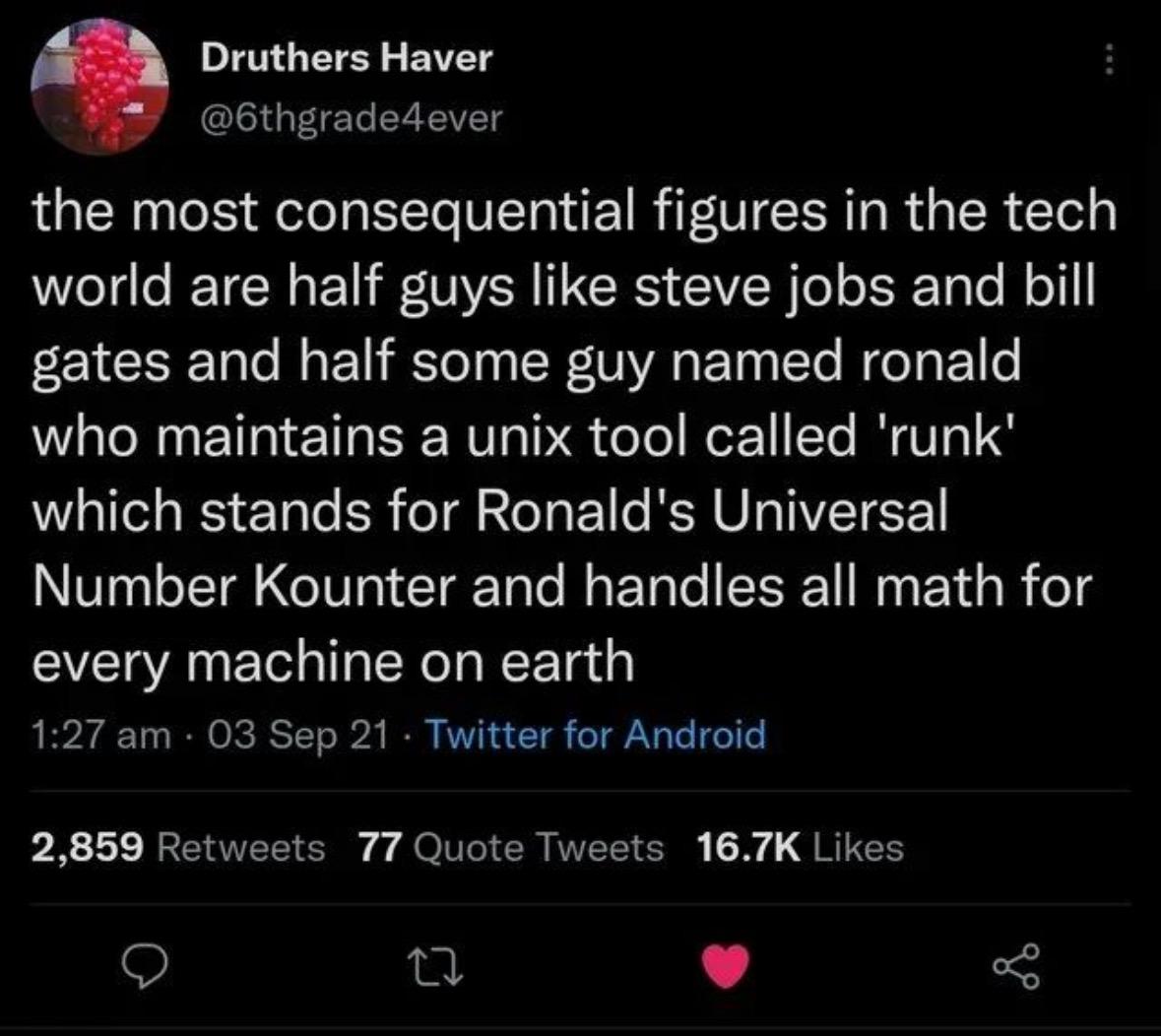
Based on my cheatsheet, GNU Coreutils, sed, awk, ImageMagick, exiftool, jdupes, rsync, jq, par2, parallel, tar and xz utils are examples of commands that I frequently use but whose developers I don't believe receive any significant cashflow despite the huge benefit they provide to software developers. The last one was basically taken over in by a nation-state hacking team until the subtle backdoor for OpenSSH was found in 2024-03 by some Microsoft guy not doing his assigned job.
I heard about that last one on a podcast and it was the first thing I thought of when I saw this post. Genuinely interesting story (if you're into that sort of thing). The pod was saying how it's both a flaw of open source that it could happen that way and an advantage because it was discoverable due to the fact that the code is open source.
Which podcast? Sounds like something I'd be interested in listening to
Also replied to another comment, sounds like this one here: https://opensourcesecurity.io/2024/04/01/xz-bonus-spectacular-episode/