There are 2 answers to this.
Security
From a security point, Firefox on Android does not isolate processes and not even itself in a good way (I will try and search up the exact reason, its some modern Android feature that Firefox supposedly does not use).
So we should assume that Firefox is less secure on mobile.
You should not use it, but use Cromite or Brave, Vanadium on GrapheneOS. Note that most FOSS "privacy browsers" that have a download size of under 100MB will use the system webview and also not be able to isolate processes.
Usability/Privacy
I use Mull and Librewolf on my Devices.
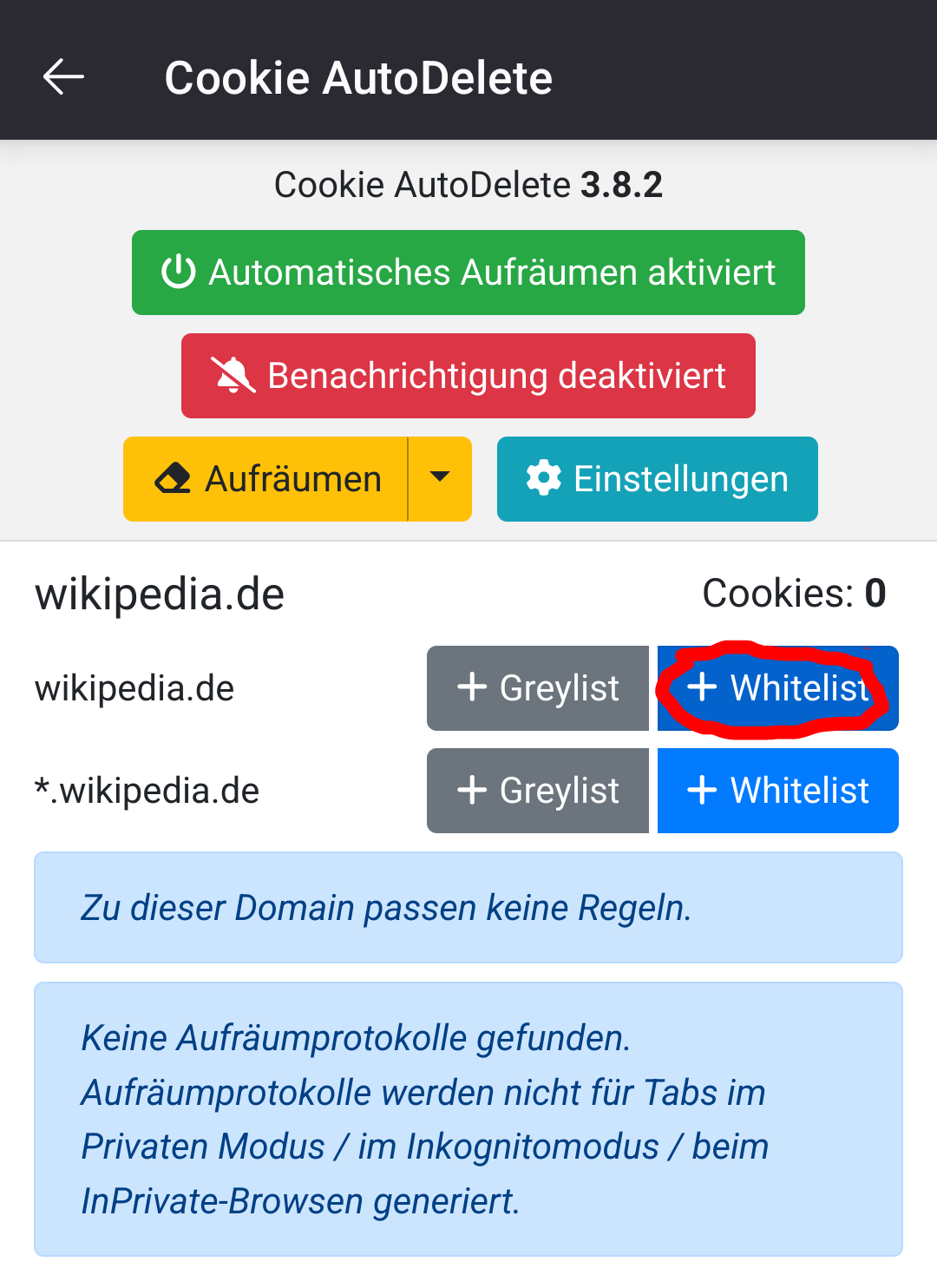
Use Mull, disable keeping history (but do not enable "delete cookies") and use "Cookie Autodelete" to replicate what Firefox desktop can. You set it to delete all cookies, but you visit sites where you want to stay logged in, open the popup and whitelist only them. You "outsource" the cookie cleaning to the addon, as FF mobile doesnt have this feature.
I do it like that on mobile and desktop, delete all cookies and only keep those where you want to stay logged in.
On Mull also install UBlock origin. If you want security and an opt-in approach, install NoScript too and set "default" to not allow any javascript. You will need to "unbreak" every site you visit.
This approach will spare you of hundreds of embedded javascripts on websites, and you manually allow only what seems okay. (You mostly never know if it really is, as Javascript is often obfuscated). This is good for privacy and security.
the theory behind this
Adblockers and malware scanners use "badness enumeration" which means "allow everything but block a, b and c". This is fundamentally flawed, as malware can easily change "how it looks" (encode and decode again, or use randomized obfuscation) and with ads you will always have to keep track of changes.
The list of malware and ad sites will grow and grow, slowing down machines and consuming tons of processes.
Noscript and the cookie approach are the opposite, you block everything and the list you keep is only as big as the stuff you want.
Please also read the more detailed words on some points, but note that I am not an Expert
I am not sure but Firefox desktop (gecko) and mobile (fenix) are separate projects. I think they share a lot of code though.
So a browser renders webpages, CSS, Javascript and nowadays even Webassembly and WebGL stuff.
If you stick to HTML and CSS you are way more secure, Javascript is way more attack surface, and JIT+Webassembly where about 50% of Microsoft Edges security vulnerabilities.
So if you disable WebGL and JIT+Webassembly by default the attack surface is way lower. But there are websites, especially good stuff like Tuta doing in-browser encryption over advanced quantum resistant protocols, that require JIT. GrapheneOS Vanadium now has a toggle to enable JIT for some sites, Edge Desktop has too afaik (dont use it but its likely the most secure browser on Windows), Chrome-ium desktop allows a policy where you can list JIT exceptions.
Firefox desktop and mobile both likely allow blocking wasm and jit in about:config but no GUI toggle yet. Torbrowser in "very secure mode" also blocks JIT.
Coming to the engine, Chrome-ium focuses a lot on sandboxing, while using C and C++ for like everything.
Firefox has the rendering engine completely rewritten in Rust.
Assuming that most sandbox escapes come from memory issues, firefoxes sandbox doesnt have to be as secure if they simply dont have memory issues as they use Rust.
Firefox Desktop uses Seccomp filters for every process (restricting syscalls the processes can make) and separates processes using unprivileged user namespaces for every process (I think they call that fission). Firefox Flatpak can only use seccomp filters but the processes are not isolated from another, which is why you should probably use a system install (binary, .deb, .rpm, ...).
You can sandbox system installed apps using bubblejail and allow access to the syscalls needed to create user namespaces. But it is pretty complicated and incomplete in my experience, even though I dont know why.
On Android firefox still uses the engine in Rust afaik, but Android has a very different model how to isolate apps. Also only Chrome-ium can isolate every process strongly on Android, yet. It is totally possible but Mozills doesnt seem to care.
At the same time to be honest I never had a security vulnerability in Firefox affect me, my entire life.
It is important to protect activists and people that "StAtE ActOrS" want to target, so those people should use the most secure browser possible.
The problem is simply that we have no privacy respecting variant on the desktop, that also has quick CI/CD updates. Ungoogled Chromium often lacks behind on Updates (and dont mention Thorium please).
This could be done by people that know how to build such a pipeline on Gitlab, Github etc. and apply all the ungoogle patches to the browser, hardening the build and creating .RPM packages every few days. There just is nobody currently doing that.