this post was submitted on 06 Oct 2024
735 points (90.8% liked)
Technology
60087 readers
2208 users here now
This is a most excellent place for technology news and articles.
Our Rules
- Follow the lemmy.world rules.
- Only tech related content.
- Be excellent to each another!
- Mod approved content bots can post up to 10 articles per day.
- Threads asking for personal tech support may be deleted.
- Politics threads may be removed.
- No memes allowed as posts, OK to post as comments.
- Only approved bots from the list below, to ask if your bot can be added please contact us.
- Check for duplicates before posting, duplicates may be removed
Approved Bots
founded 2 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
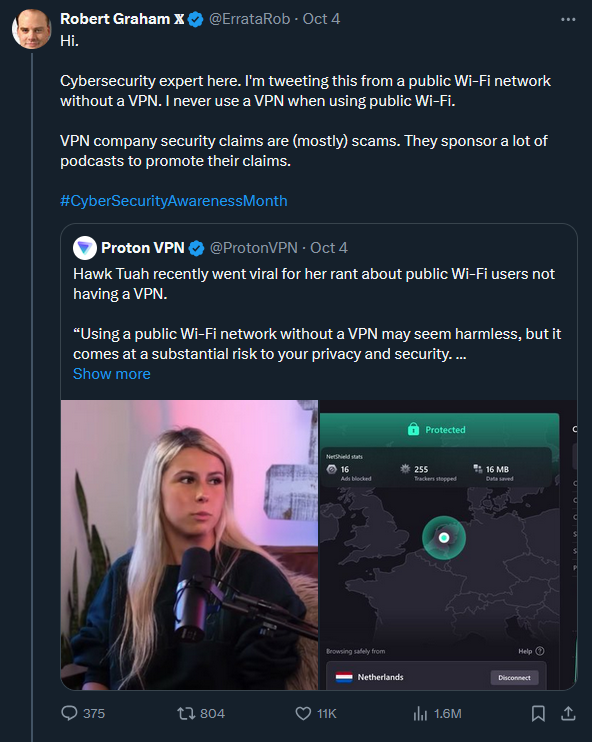
The quick and dirty answer is no, unless an attacker can figure out a way to get your VPN to strip it's encryption (doubt you'll ever see this outside something like defcon but you never know lol).
The long answer is that not all VPNs are equal depending on what you are trying to accomplish.
A VPN will simply tunnel your internet traffic over an encrypted channel to a server anywhere in the world.
On a technical level, this means that it will guarantee your internet traffic is unreadable until it hits the destination, which does mean it can make it more secure to use a public wifi/hotspot.
Of course privacy is actually a massive security iceberg, so some caveats in no particular order are:
spoiler
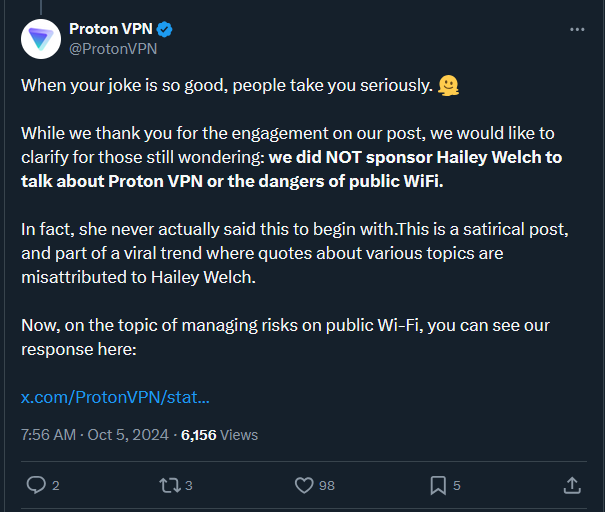
Modern protocols like HTTPS are already encrypted, although someone can still mess with stripping and poisoning techniques, so having a VPN running would be peace of mind.
Your privacy from companies like Google, Facebook, etc won't be enforced by a VPN if you don't also use a new browser session (incognito) because they can easily track your identity via cookies and accounts.
Even if you use a fresh session and dedicated VPN accounts, aforementioned tech companies can still identify you via statistical modeling based on your activity. They don't really care what your IP is unless they need to pay tax for a country or follow some random media block law.
Your privacy from the government is nonexistent because most VPN companies will share your info if the government requests it.
Lots of VPNs choose to block torrenting so they don't have to deal with protecting their customers (although lots also don't).
Even if you setup your own VPN via a VPS in anonymous way, the government can still watch your exit traffic and link the origin back to you by inspecting the VPN packets (which is why Tor exists, a much different solution to the privacy problem).
You should use a VPN if:
You should not use a VPN if:
--
After all that, the use case basically becomes: