this post was submitted on 29 Mar 2025
986 points (98.8% liked)
[Moved to !iiiiiiitttttttttttt@programming.dev, check pinned post.] iiiiiiitttttttttttt.
922 readers
2 users here now
you know the computer thing is it plugged in?
Moved to !iiiiiiitttttttttttt@programming.dev.
founded 2 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
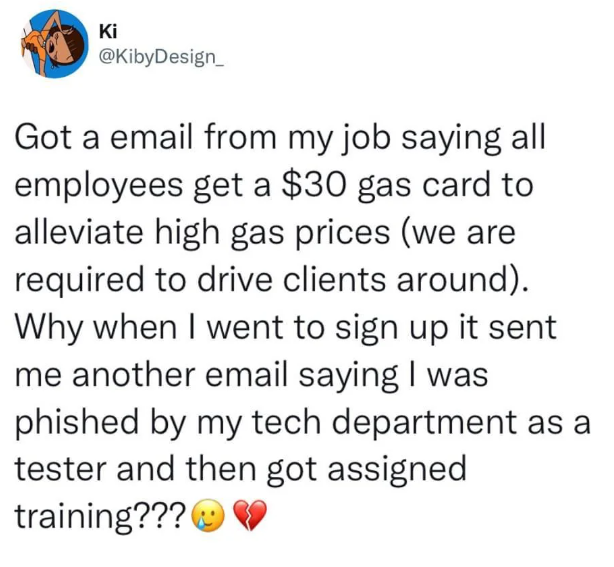
I'm on our cybersecurity team and our last phishing sim was so real looking and legit sounding I thought it was real, and I knew the phish was coming. The only indicator was the sender email was a slight misspelling of Microsoft. I pointed out that that phish is not a fair phish, our users are not going to meticulously examine every email for microscopic indicators. Half if them are barely tech literate, but they're doctors or nurses and only know what they need to know to do their job. Our cybersecurity lead was completely in "wtf are you talking about? From Micrasoft.com is totally illegitimate" mode, I had to point out that our users flag 70% of the emails as phish, and phishing tests that look like completely legitimate emails aside from a single character out of place in an obscure location most of our users aren't even thinking if looking at undermine legitimate emails and increase our workload b/c we've trained our users to think every email is a phish test from cybersecuriry.
I don’t see the problem, is that not the point of phishing tests? Users need to ensure the sender is legitimate before taking action such as clicking links.
good way to get me to ignore all emails
Yet another good idea in theory ruined by the human condition. Train people to think emails may be dangerous? Instead of critically examining each one they just ignore them to minimize risk by default. No amount of training will beat the cognative skills required for competent spam identification into most heads. Even if it could, some phising is so sophisticated in the social engineering it even tricks up cybersecurity types who should know better. Damned if you do, damned if you don't from a company perspective.
But the truth is emails may be dangerous, and the trainings exist to show people how to tell the difference. What reasonable alternative is there? Your argument is effectively “People will never learn how to use a fire extinguisher so why bother doing fire safety training. Some fires are so bad that a fire extinguisher will do nothing.” We don’t control the danger, but we can manage and minimize the risk through training.
Plain-text emails. No clickables, no tracker images.
--
Honestly, while I agree that good training is a way forward, I gotta say the training at my workplace does NOT let you know how to check anything. It's more of a "don't open emails you don't trust", here are some nightmare scenarios. While, at the same time, we get actual mandatory training emails, that are flagged by both our internal mail system, and the pre-installed mail client as "DO NOT TRUST" that we are required to click through. My complaints to IT to at least fix the internal mail system flagging have been replied to with "User's should expect these emails, so they should know to ignore all the warnings and click anyway."
We are training people to ignore their training, so of course it's not helping.
Also, even with SPF and DMARC and whatever other TXT records in place, it's still possible to get a "spoofed" From address into a user's inbox, so I find teaching people to use that header as an indicator of anything personally offensive to my technical knowledge.
Idk man, I feel like you’re striving for perfection in an imperfect world. I agree it would be nice for all email to be plain-text and with no clickables, but that’s not the world we live in, and getting companies to remove them from mandatory emails is an uphill battle.
While it’s true that there’s no way to completely eliminate spoofed “From” addresses, I think it’s fair to say it’s rare, and that checking the “From” address will conquer a significant chunk of phishing attempts. The training isn’t meant to 100% eliminate the effects of phishing attacks, it’s meant to reduce the number.
The cyber security emails in my company are so fucked up that everyone is paranoid to open up any email. Maybe it was fear. Or maybe it was collective malicious compliance. Or maybe we're all just sick of it.
A manager last week said nobody filled out a company intake form because they used a new survey software, so the url didn't look familiar.
The CFO emailed a PDF of a presentation and people were afraid to view it during meetings.
In the chat software, we are constantly going, "Is this real?"
Congrats security nerds.
Next up: All internal emails and files must be signed by the certificate that was issued to the employee sending it, if an email is send without a valid signature the E-Mail server self destructs to prevent infection.
Not to mention the fact that the majority of email clients these days don't even actually show you the full URL of the mail server that the mail is coming from. It gets obfuscated away over the display name and you have to explicitly go out of your way to actually see the full URL
This is so crazy to me. Why the hell did they start hiding the address? The one thing that can't be faked? Couldn't believe how hard it was the first time I needed to check.