this post was submitted on 22 Jul 2023
2655 points (100.0% liked)
Piracy: ꜱᴀɪʟ ᴛʜᴇ ʜɪɢʜ ꜱᴇᴀꜱ
63884 readers
341 users here now
⚓ Dedicated to the discussion of digital piracy, including ethical problems and legal advancements.
Rules • Full Version
1. Posts must be related to the discussion of digital piracy
2. Don't request invites, trade, sell, or self-promote
3. Don't request or link to specific pirated titles, including DMs
4. Don't submit low-quality posts, be entitled, or harass others
Loot, Pillage, & Plunder
📜 c/Piracy Wiki (Community Edition):
🏴☠️ Other communities
FUCK ADOBE!
Torrenting/P2P:
- !seedboxes@lemmy.dbzer0.com
- !trackers@lemmy.dbzer0.com
- !qbittorrent@lemmy.dbzer0.com
- !libretorrent@lemmy.dbzer0.com
- !soulseek@lemmy.dbzer0.com
Gaming:
- !steamdeckpirates@lemmy.dbzer0.com
- !newyuzupiracy@lemmy.dbzer0.com
- !switchpirates@lemmy.dbzer0.com
- !3dspiracy@lemmy.dbzer0.com
- !retropirates@lemmy.dbzer0.com
💰 Please help cover server costs.
 |
 |
|---|---|
| Ko-fi | Liberapay |
founded 2 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments

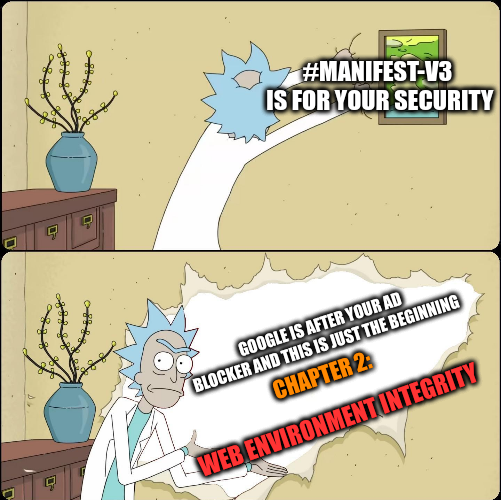
web env. integrity is not as bad as people make it out to be.
yeah I absolutely agree that it's terrible and also a bad idea (we don't need MORE drm in our browsers, I'm looking at you, Widevine (although firefox worked around it by running drm in an isolated container)), but it's main purpose is to detect automated requests and effectively block web scraping with a drm system (it ensures two things: your useragent can be trusted and you're a real non-automated user), NOT detect ad blockers. It doesn't prevent web pages from being modified like some people are saying.
there's a lot of misleading information about the api as it doesn't "verify integrity" of the web page/DOM itself.
it works by creating a token that a server can verify, for example when a user creates a new post. If the token is invalid, server may reject your attempt to do an action you're trying to perform. (this will probably just lead to a forced captcha in browsers that don't support it...)
Also, here's a solution: Just don't use Chrome or any Chromium-based browsers.
Provided your bank has not stopped supporting your "non-secure" browser. The previous browser vendor that had a functional monopoly did abuse user-agent to harass the competition. Using non IE required changing your user-agent to IE/Windows for a lot of sites.
Or as they say:
In itself it does not, yes. What it will do is tell the server if the user runs a "non-approved" system configuration. That could mean anything from using addons that were installed from outside of the chrome addon store, through running a custom chromium build, to running an unapproved operating system or an approved operating system but unapproved state (driver signature enforcement disabled, TPM not present or says the system is "not trusted").
Just like on Android with SafetyNet for the past few years. If you rooted your phone (perhaps to remove datamining bloatware from facebook and such) or straight out installed an alternative android system that respects you, then your phone is "not trusted" anymore, and a couple of apps wont work now.
We know it exactly how it will work, and with this it wont stop at the smartphone, it will spread to affect any kind of PCs too.
This will have nothing to do with the security of users. This is solely about the security of web service providers, that you won't even try to filter the content that they want to push to your device when visiting their website.
This has no place outside of the strictest of corporate environments, at all.
Sure, except that by this the server will know it exactly if your browser even allows effective adblockers (firefox) or not (chrome), and may as well decide to refuse to work if there is a possibility that the user has an ad blocker.
No, as you have written later, just using a non-chrome web browser will not be a solution, just as using banking apps and others is not possible on alternative android systems like LineageOS or GrapheneOS, not because actual incompatibility, but because of the device not being "trusted" (by google, as they run the verification system over there too).
tbf safetynet attestation can be faked
If you mean with obscure, closed source Magisk modules that can break any moment then yes, it can.
Not in Stock Android, which is what it matters.
it always succeeds in stock android
Nothing in the current proposals does either of those two things. In particular the second.